搜索结果: 1-15 共查到“理学 attack”相关记录16条 . 查询时间(0.226 秒)
Pest attack-order changes plant defenses
defenses of plants pest management virus infection
font style='font-size:12px;'>
2021/8/11
The dining time of different insects impacts a plant's defenses and nutritional quality -- a complexity uncovered in new research with implications for pest management strategies.
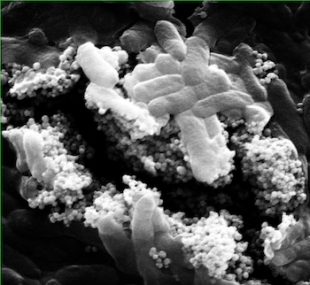
Magnetized viruses attack harmful bacteria(图)
Magnetized viruses attack harmful bacteria
font style='font-size:12px;'>
2017/9/1
Magnetic nanoparticle clusters have the power to punch through biofilms to reach bacteria that can foul water treatment systems, according to scientists at Rice University and the University of Scienc...
Source attack of decoy-state quantum key distribution using phase information
Source attack decoy-state quantum key distribution phase information
font style='font-size:12px;'>
2016/1/23
Quantum key distribution (QKD) utilizes the laws of quantum mechanics to achieve information-theoretically secure key generation. This field is now approaching the stage of commercialization, but many...
Attack Detection and Identification in Cyber-Physical Systems -- Part I: Models and Fundamental Limitations
Attack Detection Identification Cyber-Physical Systems Models Fundamental Limitations
font style='font-size:12px;'>
2012/2/29
Cyber-physical systems integrate computation, communication, and physical capabilities to interact with the physical world and humans. Besides failures of components, cyber-physical systems are prone ...
Examples of the Generalized Quantum Permanent Compromise Attack to the Blum-Micali Construction
Examples of the Generalized Quantum Permanent Compromise Blum-Micali Construction
font style='font-size:12px;'>
2011/1/19
This file contains examples of the generalized quantum permanent compromise attack to the Blum-
Micali construction. The examples presented here illustrate the attack described in the paper published...
An online attack against Wiesner's quantum money
Wiesner quantum money
font style='font-size:12px;'>
2010/10/29
Wiesner's quantum money [5] is a simple, information-theoretically secure quantum cryptographic protocol. In his protocol, a mint issues quantum bills and anyone can query the mint to authenticate a ...
nse-Coding Attack on Three-Party Quantum Key Distribution Protocols
nse-Coding Attack Three-Party Quantum Key Distribution Protocols
font style='font-size:12px;'>
2010/10/19
Cryptanalysis is an important branch in the study of cryptography, including both the classical cryptography and the quantum one. In this paper we analyze the security of two three-party quantum key d...
Avoiding the Detector Blinding Attack on Quantum Cryptography
Detector Blinding Attack Quantum Cryptography
font style='font-size:12px;'>
2010/10/21
Although the protocols used for quantum key distribution (QKD) have been proven to be unconditionally secret, the security of actual hardware depends critically on the detail of their implementation. ...
After-gate attack on a quantum cryptosystem
After-gate attack on quantum cryptosystem
font style='font-size:12px;'>
2010/10/20
We present a method to control the detection events in quantum key distribution systems that use gated single-photon detectors. We employ bright pulses as faked states, timed to arrive at the avalanch...
Rates of overgrowth by macroalgae and attack by sea anemones are greater for live coral than dead coral under conditions of nutrient enrichment
Rates of overgrowth macroalgae attack
font style='font-size:12px;'>
2014/4/18
A mesocosm experiment was conducted to determine the effects of nutrient enrichment on competitive
interactions between a hard coral, a green alga, and a sea anemone. In the low-nutrient controls, ab...
Attack of Many Eavesdroppers via Optimal Strategy in Quantum Cryptography
Eavesdroppers Optimal Strategy Quantum Cryptography
font style='font-size:12px;'>
2010/4/8
We examine a situation that $n$ eavesdroppers attack the Bennett-Brassard cryptographic protocol via their own optimal and symmetric strategies. Information gain and mutual information with sender for...
Detrended Fluctuation Analysis on Correlations of Complex Networks
Under Attack and Repair Strategy
correlations detrended fluctuation analysis complex networks
font style='font-size:12px;'>
2007/8/15
2006Vol.45No.4pp.765-768DOI:
Detrended Fluctuation Analysis on Correlations of Complex Networks
Under Attack and Repair Strategy
CHI Li-Ping, YANG Chun-Bin, MA Ke, and CAI Xu
...
Effects of alpha fetoprotein on escape of Bel 7402 cells from attack of lymphocytes.
font style='font-size:12px;'>
2007/7/28
专著信息
书名
Effects of alpha fetoprotein on escape of Bel 7402 cells from attack of lymphocytes.
语种
英文
撰写或编译
作者
Mengsen Li,Xinhua Liu,Sheng Zhou,Pingfeng Li,Gang Li
第一作者单位
出版社
BMC Cancer 2005, 5:96? (Sep ...

Scientists Image Plant “Attack” Signaling System(图)
Plant Signaling System
font style='font-size:12px;'>
2007/3/19
Britain could be paralyzed by radioactive attack(图)
radioactiv
font style='font-size:12px;'>
2007/2/10


